Over the past half decade, the Emotet malware has emerged as a top Internet threat that pillages people’s bank accounts and installs other types of malware. The sophistication of its code base and its regularly evolving methods for tricking targets into clicking on malicious links—in September, for instance, it began a spam run that addresses recipients by name and quotes past emails they sent or received—has allowed it to spread widely. Now, Emotet is adopting yet another way to spread: using already compromised devices to infect devices connected to nearby Wi-Fi networks.
Last month, Emotet operators were caught using an updated version that uses infected devices to enumerate all nearby Wi-Fi networks. It uses a programming interface called wlanAPI to profile the SSID, signal strength, and use of WPA or other encryption methods for password-protecting access. Then, the malware uses one of two password lists to guess commonly used default username and password combinations.
After successfully gaining access to a new Wi-Fi network, the infected device enumerates all non-hidden devices that are connected to it. Using a second password list, the malware then tries to guess credentials for each user connected to the drive. In the event that no connected users are infected, the malware tries to guess the password for the administrator of the shared resource.
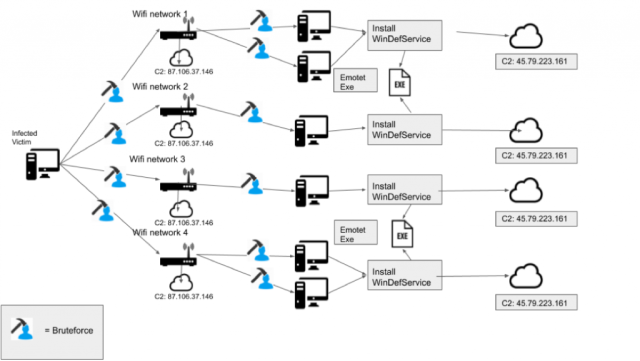
While Emotet is best known for circulating through malicious email runs, it has also been observed spreading in worm-like fashion from device to device over infected networks. If it successfully guesses the password to a connected device, it then loads the Emotet malware and possibly other pieces of malware—such as the Ryuk ransomware or the TrickBot malware—in exchange for fees paid by operators of those campaigns. No longer content with infecting only devices inside the compromised network, Emotet is now using the newly discovered version to jump from network to network.
Beware of weak passwords
“With this newly discovered loader-type used by Emotet, a new threat vector is introduced to Emotet’s capabilities,” researchers from security firm Binary Defense wrote in a recently published post. “Previously thought to only spread through malspam and infected networks, Emotet can use this loader-type to spread through nearby wireless networks if the networks use insecure passwords.”
The Binary Defense post said the new Wi-Fi spreader has a timestamp of April 2018 and was first submitted to the VirusTotal malware search engine a month later. While the module was created almost two years ago, Binary Defense didn’t observe it being used in the wild until last month.
The newly documented spreader underscores the importance of using strong passwords to restrict access to Wi-Fi networks. Emotet’s previously known ability to spread from device to device within a network already underscored the importance of using strong passwords to restrict access to devices connected to local networks. Passwords should always be randomly generated and should never be fewer than 11 characters.
One aspect of the new Wi-Fi spreader is out of keeping with Emotet’s usual penchant for stealth of sophistication. The module uses unencrypted connections to communicate with attacker-controlled servers. That makes it easy to detect patterns in traffic that people can use to detect infections. The malware can also be detected through active monitoring of connected devices for new services being installed and watching for any processes or services running from temporary files and user profile application data folders. The Binary Defense post provides other indicators of compromise.



