Researchers said they recently discovered a zero-day vulnerability in the 7-Zip archiving utility that was actively exploited as part of Russia’s ongoing invasion of Ukraine.
The vulnerability allowed a Russian cybercrime group to override a Windows protection designed to limit the execution of files downloaded from the Internet. The defense is commonly known as MotW, short for Mark of the Web. It works by placing a “Zone.Identifier” tag on all files downloaded from the Internet or from a networked share. This tag, a type of NTFS Alternate Data Stream and in the form of a ZoneID=3, subjects the file to additional scrutiny from Windows Defender SmartScreen and restrictions on how or when it can be executed.
There’s an archive in my archive
The 7-Zip vulnerability allowed the Russian cybercrime group to bypass those protections. Exploits worked by embedding an executable file within an archive and then embedding the archive into another archive. While the outer archive carried the MotW tag, the inner one did not. The vulnerability, tracked as CVE-2025-0411, was fixed with the release of version 24.09 in late November.
Tag attributes of outer archive showing the MotW.
Credit:
Trend Micro
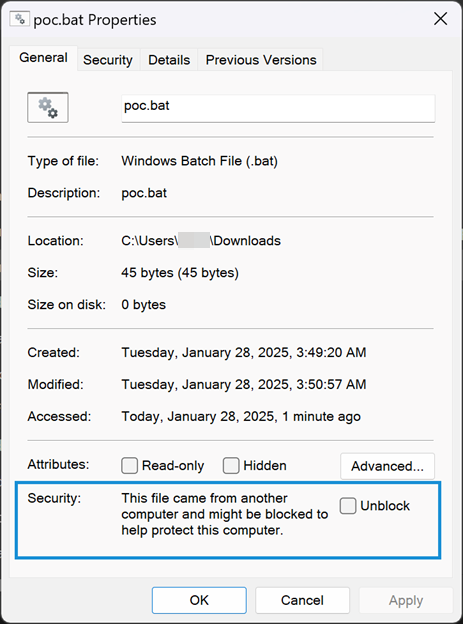
Attributes of inner-archive showing MotW tag is missing.
Credit:
Trend Micro
“The root cause of CVE-2025-0411 is that prior to version 24.09, 7-Zip did not properly propagate MoTW protections to the content of double-encapsulated archives,” wrote Peter Girnus, a researcher at Trend Micro, the security firm that discovered the vulnerability. “This allows threat actors to craft archives containing malicious scripts or executables that will not receive MoTW protections, leaving Windows users vulnerable to attacks.”



