If you reuse passwords across multiple accounts, you’re not alone. A recent Forbes Advisor study found that, on average, Americans reuse the same password for at least four accounts. This is despite reused passwords accounting for approximately 30% of compromised passwords in 2024. Of course, this is nothing new, tales of data breaches occur every year, prompting yet another focus on how poor our passwords are at protecting our accounts. Attempts to replace passwords with passkeys are ongoing, but passwords are here to stay for the foreseeable future, and so are their vulnerabilities.
Google has been attempting to improve our password practices for years, but as the Forbes Advisor study shows, little has changed. Google’s latest attempt is its boldest yet, using Gemini to replace compromised passwords automatically. However, this could do more harm than good.
How is Google using Gemini to protect your passwords?
Google suggests you won’t need to remember your passwords ever again
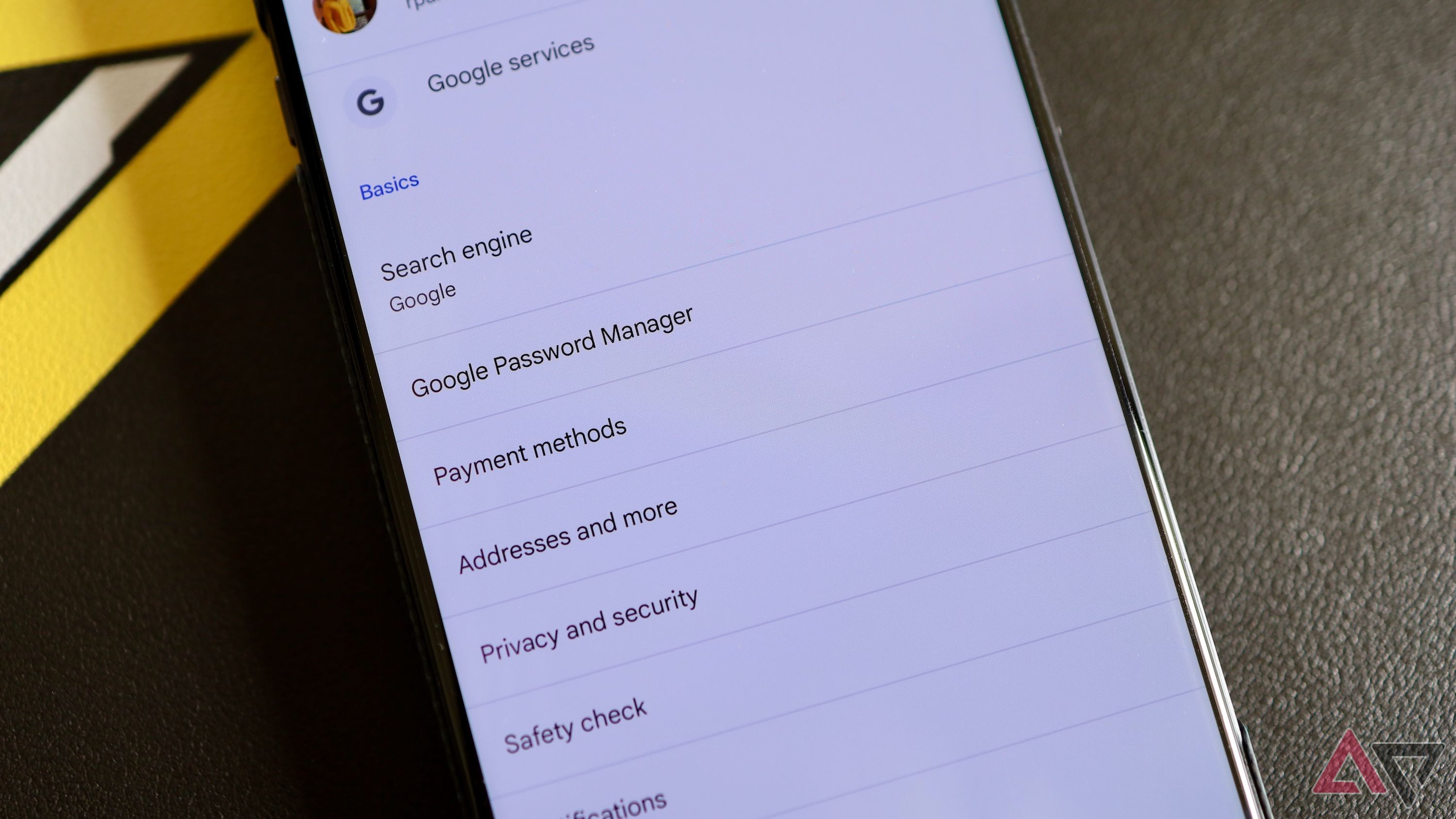
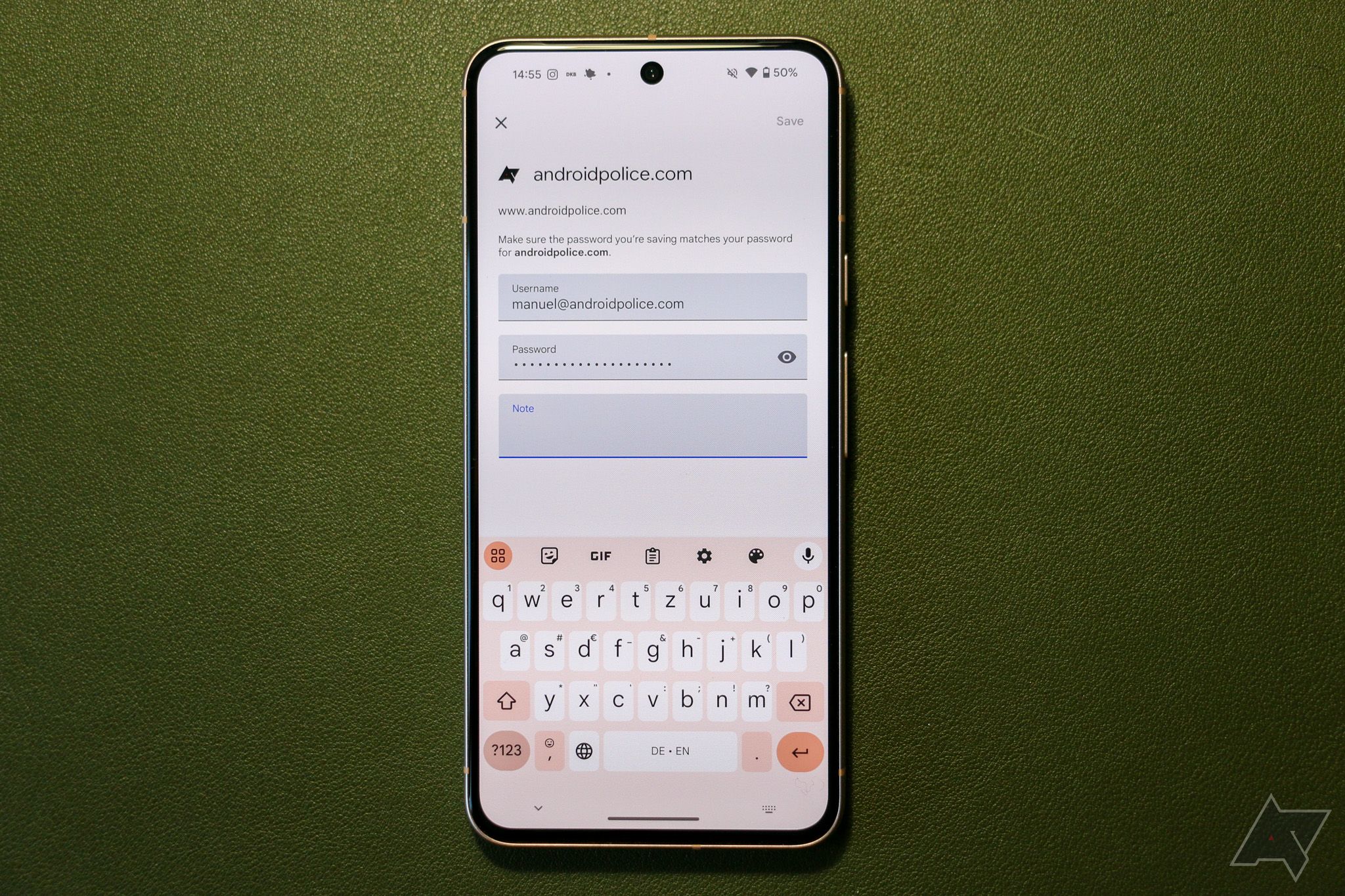
Google Chrome’s integrated password manager has long provided us with all the tools you need to create and store secure passwords. Google Password Manager (GPM) can auto-generate strong passwords (although these are only available across devices you’ve signed into your Google account with), and it will alert you of any data breaches involving your accounts.
However, GPM can only make suggestions. If you don’t use its suggested passwords and ignore alerts of data breaches, then you are vulnerable to malicious hackers.
Google attempts to fix this problem in the same way it’s “solving” many other issues we encounter in our digital lives. That is, of course, by ramming Gemini into as many products as possible, and damn the consequences. This upgrade for GPM will let the password manager detect and replace compromised passwords with minimal user intervention.
This feature is still in development, and Google hasn’t clarified exactly how it will work. But even if it works perfectly, it may not help reduce the rate at which accounts are compromised.
A Gemini-powered password manager will still be susceptible to human error
AI can’t fix our tendency to create weak passwords
Let’s say that Google overcomes any issues implementing this feature, and Gemini can successfully replace compromised passwords. What would this look like in reality?
The most obvious result is that Google automatically creates a strong password using its existing method of a long mixture of letters, numbers, and special characters. These passwords are secure but impossible to remember. If you want to access your account somewhere where Google Password Manager doesn’t operate (i.e., Microsoft Edge or Firefox), then you’ll need to type it in manually.
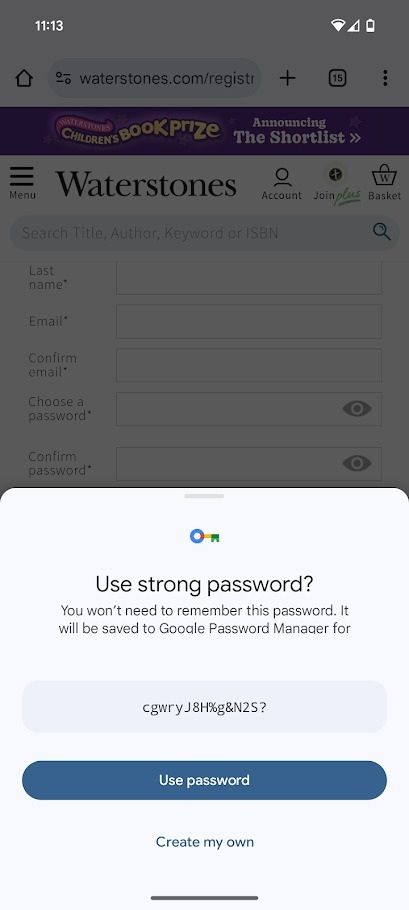
The chain of events after your password is compromised is obvious. Your account is compromised, and Google automatically replaces it. Unfortunately, you don’t need to remember it, so when you log in to your account outside of Chrome or Android, you have to change the password. You thus need to change the password to something you remember. Can you see where this is going?
Of course, you can’t reuse a password on most websites. The most common tactic is to add a single number or digit, which is ineffective and can lead to another compromised account, this renders the entire system useless.
You can’t rely on Google Password Manager
GPM isn’t as secure as you think
Google’s answer to the previous scenario would be something like: “Just use Chrome and Android!” But apart from the fact that it’s impossible to solely use Chrome and Android for our whole lives, GPM just isn’t secure enough. Even if Gemini replaces compromised passwords before malicious hackers take advantage of your breached account, the passwords are still stored in GPM.
GPM has two major flaws, which mean those fancy Gemini-generated passwords aren’t as secure as you think. Firstly, your passwords are only as secure as your phone. If you set up a PIN unlock for your phone, unsavory characters have access to GPM just from your PIN.
Secondly, GPM doesn’t have a master password. Secure password managers use biometric recognition to authenticate users. When that fails, you have a master password to access your account. GPM, on the other hand, uses the same login as your Google account. Thus, your passwords are only as secure as your Google account. And when new malware is identified that can bypass your Google passwords entirely, your passwords suddenly don’t look so secure.
Thirdly, GPM doesn’t have on-device encryption enabled by default. This basic security step would prevent malicious actors from accessing your passwords even if Google’s servers were breached. That’s right, by default, your passwords are stored unencrypted in GPM.
Related
How Gemini could make GPM less secure
Google is using Gemini to create a false sense of security
Source: Android Police / Joshua Sharpe
Let’s not be too harsh on Gemini for the moment. Immediately replacing a compromised password is a crucial step that many people don’t take, so automatically replacing your passwords is useful.
However, as we’ve discussed, GPM is a weak password manager. It lacks the basic security methods of other password managers, and it is heavily susceptible to human error.
Worse, this initiative could reassure users that their passwords are secure with Gemini. Google is suggesting that we can give up all our responsibility for creating and maintaining our passwords to Gemini. But if Google doesn’t take steps to improve GPM’s security, this new feature could create a false sense of security.
Google needs to focus on passkeys, not Gemini
Google’s blind rush to implement Gemini into its services is a mixed success. Until now, Gemini has been a relatively forgettable tool. If you don’t want to use it, you won’t suffer.
However, if Google attempts to force Gemini into high-risk services like Google Password Manager, there could be devastating compromises. Instead, it should focus on replacing our passwords with passkeys, which are proven to be more secure.