There are many reasons you might want to keep people from viewing your data. Maybe it contains sensitive information, or it could be harmful if the wrong person sees it. No matter what the reason, online privacy will always remain a legitimate concern. While many privacy-protecting features are found in iPhones and many of the top Android phones, not all of those features work when you use third-party apps. End-to-end encryption, however, is a fairly effective privacy tool that is becoming increasingly popular in messaging apps.
But what exactly is end-to-end encryption? How can it keep other people from seeing your data? In short, it’s a way of scrambling data on your device before it is sent. It does so in a way that only allows the intended recipient to decode the message. Even if a messaging app stores your scrambled message on its servers or if an unwanted third party intercepts the scrambled message, the encrypted data is useless on its own. The only person who can decode the scrambled message (theoretically, at least) is the person you sent your message to.
End-to-end encryption’s public and private keys
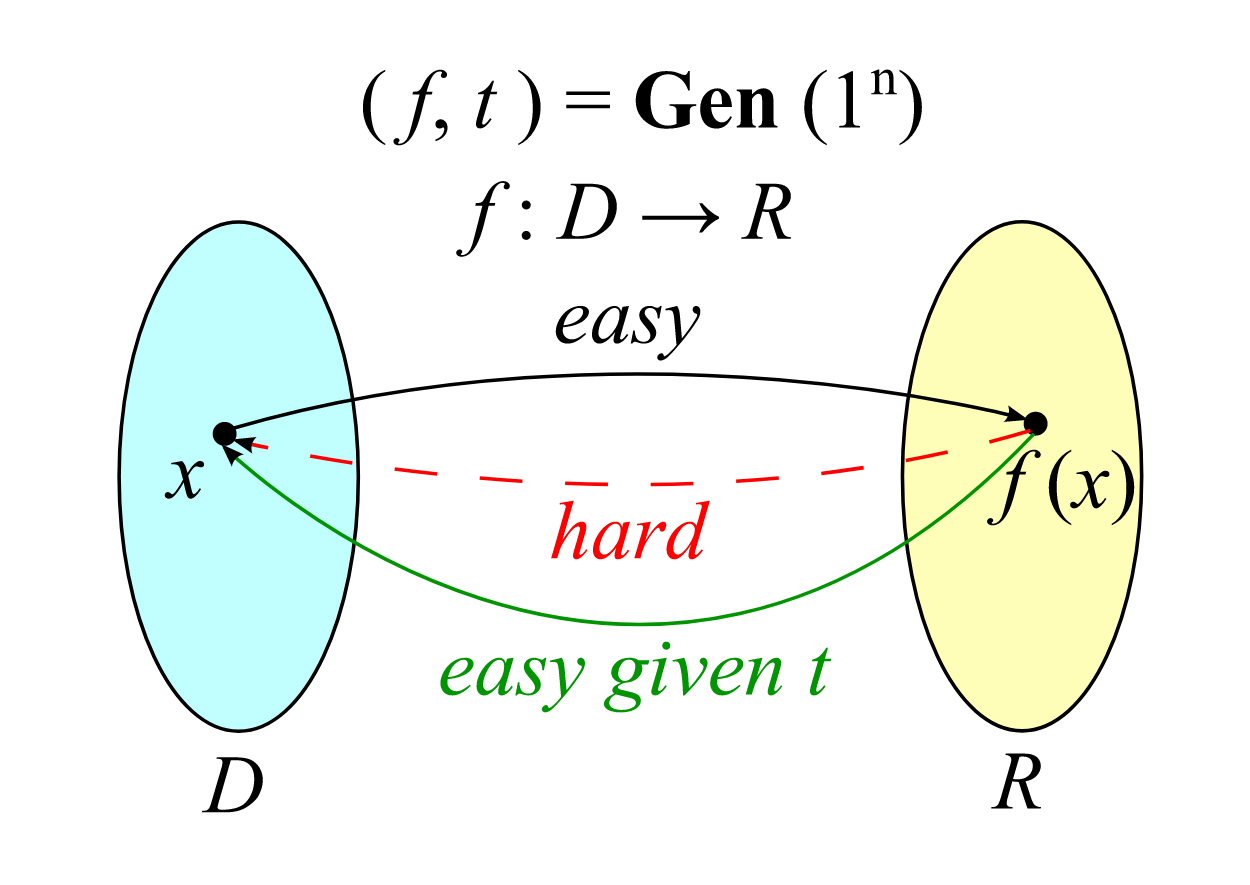
Every person who uses end-to-end encryption has two numbers called “keys.” One key is the “public key,” which anyone can see. The second key, the “private key,” is kept secret from everyone, including the app’s creators. The public key is used to encode a message, and this encoded message can only be decoded using its corresponding private key.
Source: Wikimedia Commons / rahmatagungj
When somebody sends you an encrypted message, their app uses your public key to encrypt the message. The encrypted message is sent over the internet. However, the public key can’t be used to translate the message into its original form. To do that, you need your private key. This is possible because the public key and private key are linked in a way that is nearly impossible to figure out when looking at the public key alone.
The fancy math behind end-to-end encryption
Technology, as it exists today, can’t figure out someone’s private key. The trick to the process is this: Figuring out someone’s private key is borderline impossible using current technology. Generating the two keys involves using a one-way function. This one-way function is a calculation that is easy for a computer to perform but takes a huge amount of computing power to reverse. Reversing the function becomes nearly impossible when these functions are performed on large enough numbers, such as a 64-digit private key.
Source: Wikimedia Commons / IkamusumeFan
One simple type of one-way function is to take a number, square that number, divide it by the product of two prime numbers, and take the remainder. If you know the two prime numbers, it’s easy to reverse the function and figure out the original number. However, it requires brute force to figure out the original number without the prime numbers. If the two prime numbers are large enough, no computer in the world has the computational power needed to brute force the answer.
Finding someone else’s private key makes it easy to decrypt a message. Many apps frequently switch users’ private and public keys to mitigate this issue. Discovering a user’s private key for one of these apps only decodes a few messages. The rest remain encrypted and unintelligible.
Which communication apps use end-to-end encryption?
It’s one thing to know what end-to-end encryption is. But that information is hardly useful if you don’t know which apps use it. The following apps have end-to-end encryption either as an option or enabled by default.
Signal
Signal is a unique messaging app. Not because of its features but because of its underlying philosophy. The free app, which has end-to-end encryption for all its messages, was made by the nonprofit Signal Foundation. This foundation has the stated goal of developing open source privacy technology for communications. Because of this, Signal is an open source app, as is its underlying encryption protocol called the Signal Protocol. This protocol has been used by multiple other apps, including Meta’s WhatsApp, Google’s now-defunct Allo, and Microsoft’s Skype.
Threema
Threema is another messaging app with end-to-end encryption enabled for all its messages. However, the philosophy driving Threema’s creators, the swill company Threema GmbH, couldn’t be more different from Signal’s. Threema is a proprietary app, so the exact way it functions isn’t open to the public. It’s also a paid app, meaning you must fork out $5.00 to use it. Threema also offers a self-hosted version of its software that companies can install on their own servers if they need extra security.
WhatsApp is the world’s most popular messaging and video chat app, with about two billion monthly active users across the globe. While it’s decently popular in the United States, the residents of some countries use it as their primary messaging app almost exclusively. For example, 96% of South Africans use WhatsApp, as do 93% of Argentinians and 91% of Brazilians.
WhatsApp uses the same end-to-end encryption protocol as Signal. The app automatically enables this encryption for its messaging and business messaging functions, and you can turn on end-to-end encryption for your message backups.
Telegram
Unlike Signal, Threema, and WhatsApp, Telegram does not automatically enable end-to-end encryption for its users. However, secret chats use end-to-end encryption. This type of chat can only be used when the recipient is online. Telegram has other privacy-conscious features, such as self-destruct timers that erase secret messages and a setting that automatically deletes your account after a set period of inactivity.
Facebook Messenger
Since Meta owns Facebook and WhatsApp, it shouldn’t be a surprise that Facebook Messenger has end-to-end encryption. However, unlike WhatsApp, Facebook’s end-to-end encryption capability doesn’t apply to all messages. To enable end-to-end encryption in Facebook Messenger, you have to click the “i” button in the upper-right corner of an existing conversation, then choose the option to turn on secret conversations. Secret conversations also have the option to delete messages automatically after a set period of time.
Wire
While most of the apps above only offer end-to-end encryption for messages, Wire has a wider range of communications that it can encrypt. Along with messages, Wire can apply end-to-end encryption to its file-sharing, voice calls, video calls, and conference calls with up to 25 other people at once. Wire also has team collaboration capabilities, which are also end-to-end encrypted.
Google Messages
Google’s default texting app for Android devices is a recent addition to the list of apps with end-to-end encryption. While the end-to-end encryption capability is currently in beta, Android users can use the beta version by selecting the Become a tester option from the play store. If both parties to a conversation have chat features enabled, all messages and eligible attachments are automatically end-to-end encrypted.
End-to-end encryption is not perfect
When you hear about the technology behind end-to-end encryption, it might be tempting to assume that it’s unbeatable. However, there are more things to keep in mind besides the cryptography. It can be easily bypassed, for example, by someone who has access to your phone and knows your password. People who fall prey to phishing attacks are also vulnerable, no matter how many of their apps have end-to-end encryption.
End-to-end encryption also doesn’t protect you from dishonest developers. A company can claim that it provides end-to-end encryption, but it may have implemented it improperly or added a backdoor that allows outsiders to read your messages. Ultimately, you have to be able to trust the app developer for end-to-end encryption to be at all useful.
More ways to protect yourself
Encryption is one of many ways to keep your privacy intact online. Other useful steps you can take involve enabling two-factor authentication, opting out of data collection when possible, and opting out of targeted advertising. Our article about how to enhance privacy on your Android phone is a good place to start when it comes to learning what you can do to keep your data safe, or at least as safe as possible, in this modern world.



.png)